How to configure istio (or envoy) to act as a forward proxy

Emma Payne
Published Jan 17, 2026
I have a running nginx server that has a relatively simple config (only including relevant parts):
http { server { gzip on; set $allowed false; if ($http_host ~ "(domain1.com)|(domain2.net)|(etc)") { set $allowed true; } if ($allowed = false) { return 403; break; } listen 8888; server_name ~.+; proxy_connect; proxy_max_temp_file_size 0; resolver 8.8.8.8; location / { proxy_pass proxy_set_header Host $http_host; } } } so basically if a client connects to one of the approved domains - response is streamed. I'm really struggling to achieve the same in Envoy. whatever I do it either doesnt work or doesnt forward static content. Another issue I have is if I configure my laptop to use envoy as a proxy - nothing works at all (ie even if connect to domain1.com works, if I try to connect to the same site, but using envoy as a proxy - I get a timeout), whereas the configuration above works as a proxy.
My actual target is Istio, but I'm quite confident I can port it to Istio if I figure out the envoy part
edit: sample istio config that does work for forwarding, but doesnt work as a proxy
--- apiVersion: kind: Gateway metadata: name: fwd namespace: default spec: selector: istio: ingressgateway # use istio default controller servers: - port: number: 80 name: http protocol: HTTP hosts: - "*" --- apiVersion: kind: ServiceEntry metadata: name: fwd namespace: default spec: hosts: - test.domain.com ports: - number: 443 name: tls protocol: tls location: MESH_EXTERNAL resolution: DNS --- apiVersion: kind: VirtualService metadata: name: fwd namespace: default spec: hosts: - source.domain.com gateways: - fwd http: - match: - gateways: - fwd port: 80 uri: prefix: / route: - destination: host: test.domain.com port: number: 443 --- apiVersion: kind: DestinationRule metadata: name: fwd namespace: default spec: host: test.domain.com trafficPolicy: loadBalancer: simple: ROUND_ROBIN portLevelSettings: - port: number: 443 tls: mode: SIMPLE edit 2: actually found sample envoyconfig
{ "admin": { "access_log_path": "/tmp/admin_access.log", "address": { "socket_address": { "address": "0.0.0.0", "port_value": 9901 } } }, "static_resources": { "clusters": [ { "name": "backend", "type": "SIMPLE", "connect_timeout": "0.25s", "lb_policy": "ROUND_ROBIN", "max_requests_per_connection": 1024, "max_retries": 3, "http2_protocol_options": {} } ], "listeners": [ { "name": "listener_0", "address": { "socket_address": { "address": "0.0.0.0", "port_value": 8000 } }, "filter_chains": [ { "filters": [ { "name": "envoy.http_connection_manager", "config": { "codec_type": "auto", "stat_prefix": "ingress_http", "route_config": { "virtual_hosts": [ { "name": "backend", "domains": [ "*" ], "routes": [ { "match": { "prefix": "/" }, "route": { "cluster": "backend" } } ] } ] }, "http_filters": [ { "name": "envoy.router", "config": { "use_remote_address": true, "dynamic_route_config": { "grpc_service": { "envoy_grpc": { "cluster_name": "backend" } } } } } ] } } ] } ] } ] } } 2 Answers
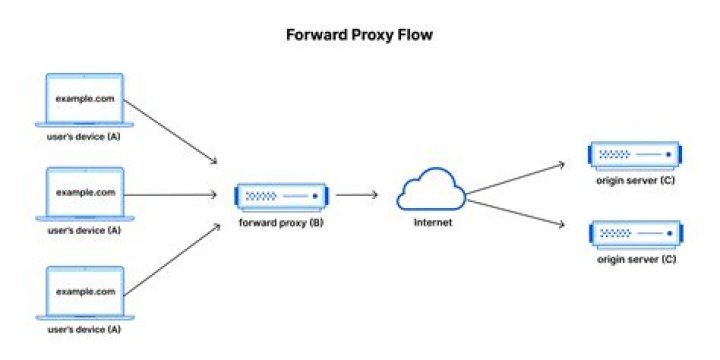
Istio-enabled pod’s outbound traffic is redirected to its sidecar proxy by default, accessing the URLs which are outside the cluster requires some modifications in the configuration of the proxy. The basic or default configuration of Istio and Envoy proxy allows traffic from unknown services to pass through, although this is the easiest way for getting started with Istio it is always recommended to enforce strict policies as per the security standpoint.
In this document it is elaborated how to access external services in different ways, refer this for more information.
2Answer provided by Kranthiveer Dontineni almost works:
admin: address: socket_address: protocol: TCP address: 127.0.0.1 port_value: 9901 static_resources: listeners: - name: listener_0 address: socket_address: protocol: TCP address: 0.0.0.0 port_value: 10000 filter_chains: - filters: - name: envoy.filters.network.http_connection_manager typed_config: "@type": stat_prefix: ingress_http route_config: name: local_route virtual_hosts: - name: local_service domains: ["*"] routes: - match: prefix: "/force-host-rewrite" route: cluster: dynamic_forward_proxy_cluster typed_per_filter_config: envoy.filters.http.dynamic_forward_proxy: "@type": host_rewrite_literal: - match: prefix: "/" route: cluster: dynamic_forward_proxy_cluster http_filters: - name: envoy.filters.http.dynamic_forward_proxy typed_config: "@type": dns_cache_config: name: dynamic_forward_proxy_cache_config dns_lookup_family: V4_ONLY typed_dns_resolver_config: name: envoy.network.dns_resolver.cares typed_config: "@type": resolvers: - socket_address: address: "8.8.8.8" port_value: 53 dns_resolver_options: use_tcp_for_dns_lookups: true no_default_search_domain: true - name: envoy.filters.http.router typed_config: "@type": clusters: - name: dynamic_forward_proxy_cluster lb_policy: CLUSTER_PROVIDED cluster_type: name: envoy.clusters.dynamic_forward_proxy typed_config: "@type": dns_cache_config: name: dynamic_forward_proxy_cache_config dns_lookup_family: V4_ONLY typed_dns_resolver_config: name: envoy.network.dns_resolver.cares typed_config: "@type": resolvers: - socket_address: address: "8.8.8.8" port_value: 53 dns_resolver_options: use_tcp_for_dns_lookups: true no_default_search_domain: true transport_socket: name: envoy.transport_sockets.tls typed_config: "@type": common_tls_context: validation_context: trusted_ca: {filename: /etc/ssl/certs/ca-certificates.crt} ncG1vNJzZmirpJawrLvVnqmfpJ%2Bse6S7zGiorp2jqbawutJobm1xYWx%2BdX6OoaawZaSkeqS7zZ%2BgoK2imnqqv9OipmanomKyr8LOsmStp12WsLV5wKxkmmWWpL%2B4rdGdZKmqn63G